Handling SSE-KMS in S3 Replication: Challenges and Solutions
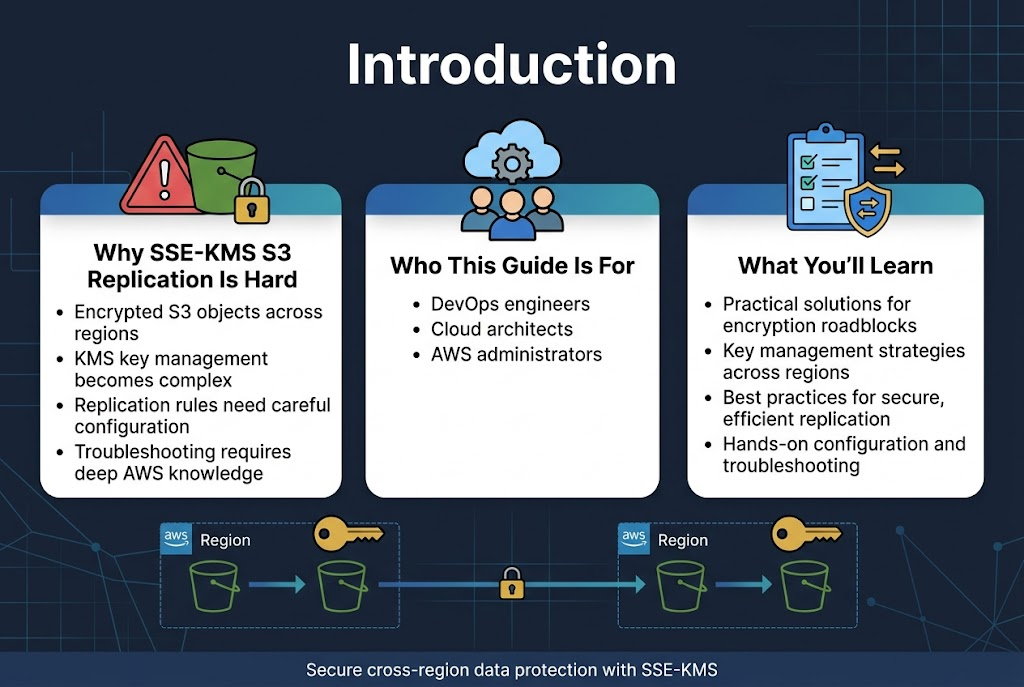
Amazon S3 cross-region replication with SSE-KMS encryption creates unique challenges that can frustrate even experienced AWS engineers. When you’re replicating encrypted S3 objects across regions, KMS key management becomes complex, replication rules need careful configuration, and troubleshooting failures requires deep understanding of how encryption and replication work together.
This guide is for DevOps engineers, cloud architects, and AWS administrators who need to implement S3 SSE-KMS replication while maintaining security and performance. You’ll learn practical solutions to overcome encryption-related replication roadblocks and establish reliable cross-region data protection.
We’ll walk through the core SSE-KMS encryption challenges that break replication, explore key management strategies that actually work across multiple regions, and share proven best practices for secure and efficient SSE-KMS replication. You’ll also get hands-on configuration steps and troubleshooting techniques to resolve common S3 replication failures when encryption is involved.
Understanding SSE-KMS Encryption in Amazon S3
Key Management Service Integration Benefits
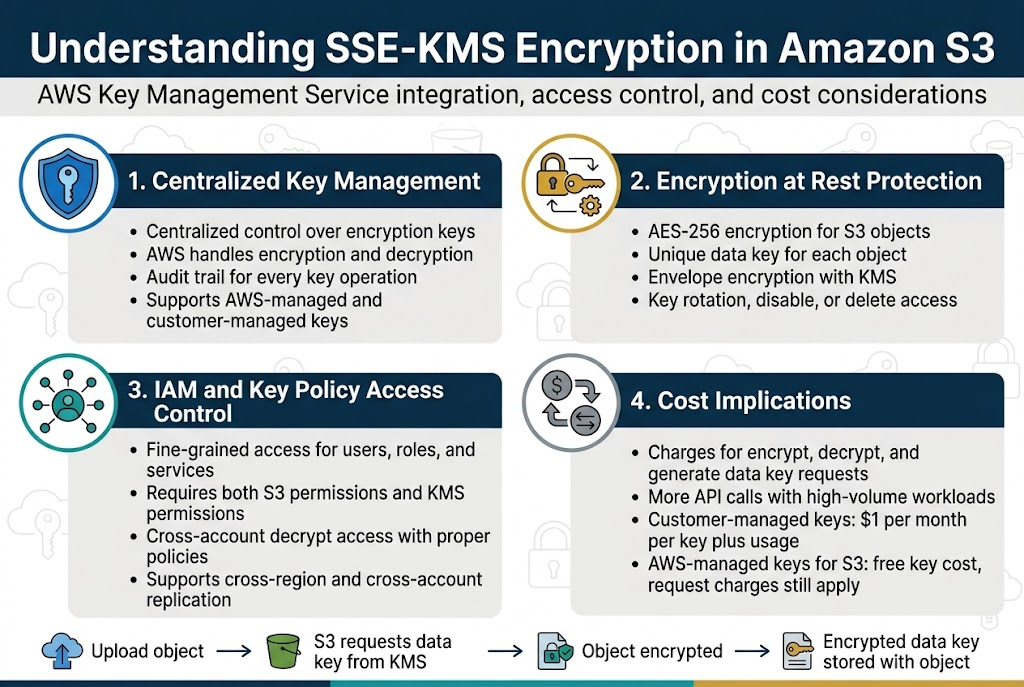
AWS KMS integration with S3 SSE-KMS encryption provides centralized control over encryption keys across your entire infrastructure. When you enable SSE-KMS for S3 objects, AWS automatically handles the complex encryption and decryption processes while giving you granular control over who can access your data. This integration creates an audit trail for every key operation, making compliance requirements much easier to meet.
The seamless integration between S3 and KMS means your applications don’t need to manage encryption keys directly. Instead, S3 handles all cryptographic operations using your specified KMS keys, whether they’re AWS-managed or customer-managed keys.
Encryption at Rest Protection Mechanisms
SSE-KMS encryption protects your S3 objects using AES-256 encryption with unique data keys for each object. When you upload an object, S3 requests a data key from KMS, uses it to encrypt your object, then stores the encrypted data key alongside your object. This envelope encryption approach means your actual encryption keys never leave KMS unencrypted.
The protection mechanism extends beyond simple encryption – KMS keys can be rotated automatically, and you can disable or delete keys to prevent future access to encrypted data. This multi-layered security approach makes SSE-KMS particularly valuable for sensitive data that requires strict access controls.
Access Control Through IAM Policies
IAM policies work together with KMS key policies to create fine-grained access controls for your encrypted S3 objects. You can specify which users, roles, or services can use specific KMS keys for encryption and decryption operations. This dual-layer permission system means users need both S3 permissions and KMS key permissions to access encrypted objects.
Cross-account access becomes straightforward with proper IAM and key policy configuration. You can grant other AWS accounts permission to decrypt objects using your KMS keys, making S3 cross-region replication with SSE-KMS possible across different AWS accounts.
Cost Implications of KMS Key Usage
SSE-KMS encryption introduces additional costs beyond standard S3 storage fees. AWS charges for KMS key usage based on the number of API requests, including encrypt, decrypt, and generate data key operations. Each S3 object operation that involves encrypted objects triggers KMS API calls, which can add up quickly in high-volume environments.
Customer-managed KMS keys cost $1 per month per key, plus usage charges for API requests. AWS-managed keys for S3 are free, but you still pay for the API request usage. Understanding these cost patterns helps you make informed decisions about when to use SSE-KMS versus other encryption options for your S3 replication strategy.
Common Challenges in S3 Cross-Region Replication with SSE-KMS
Key Access Permissions Across AWS Regions
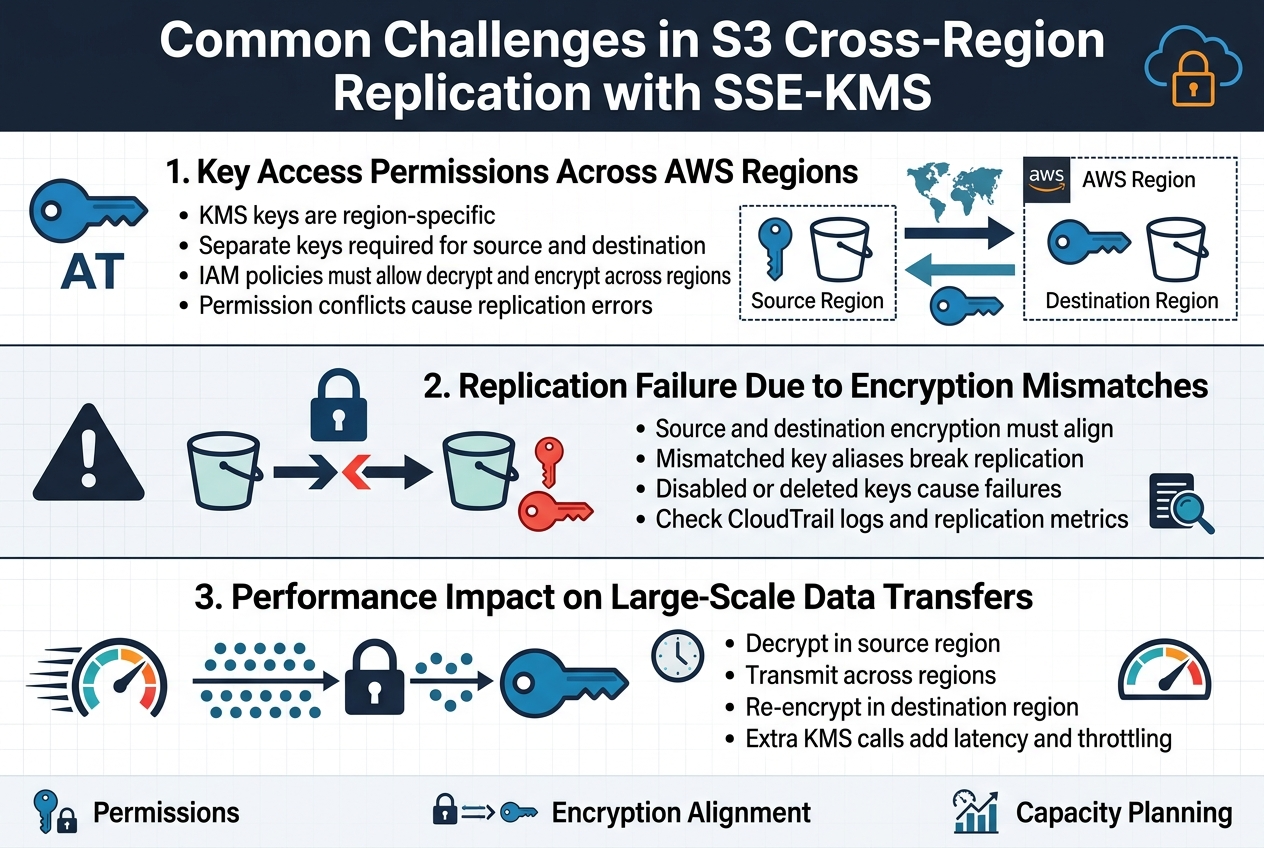
Managing KMS key permissions across multiple AWS regions creates significant complications for S3 cross-region replication. When source and destination buckets reside in different regions, you need separate KMS keys for each location since AWS KMS keys are region-specific resources. The replication process requires precise IAM policies that grant cross-region access to both source and destination keys, often leading to permission errors when policies don’t account for multi-region key usage patterns.
Setting up proper cross-region KMS permissions involves configuring key policies that allow the replication service role to decrypt objects in the source region and encrypt them using the destination region’s key. Many organizations struggle with the complexity of managing these distributed permissions, especially when dealing with multiple AWS accounts or when key policies conflict with existing security frameworks.
Replication Failure Due to Encryption Mismatches
SSE-KMS replication failures frequently occur when encryption configurations between source and destination buckets don’t align properly. Objects encrypted with customer-managed keys in the source bucket require corresponding KMS keys in the destination region, and mismatched key configurations cause replication jobs to fail silently. The challenge intensifies when different encryption methods are used across regions or when key aliases don’t match between source and destination environments.
Troubleshooting these encryption mismatches requires careful analysis of CloudTrail logs and S3 replication metrics. Common scenarios include attempting to replicate objects encrypted with disabled or deleted KMS keys, using incorrect key ARNs in replication configurations, or failing to properly configure server-side encryption settings for the destination bucket that match the source encryption requirements.
Performance Impact on Large-Scale Data Transfers
S3 SSE-KMS replication introduces additional latency compared to standard replication due to the extra encryption and decryption operations required during the transfer process. Each object must be decrypted in the source region using the original KMS key, transmitted across regions, then re-encrypted in the destination region with the target KMS key. This double encryption process can significantly slow down replication speeds, particularly for large datasets or high-frequency write operations.
The performance impact becomes more pronounced when dealing with millions of small objects or when KMS key usage limits are approached. Organizations often experience throttling issues during peak replication periods, as KMS API calls for encryption operations count against service quotas. Planning for adequate KMS request capacity and implementing appropriate retry mechanisms becomes critical for maintaining consistent replication performance across regions.
Key Management Strategy for Multi-Region Replication
Creating Regional KMS Keys for Optimal Performance
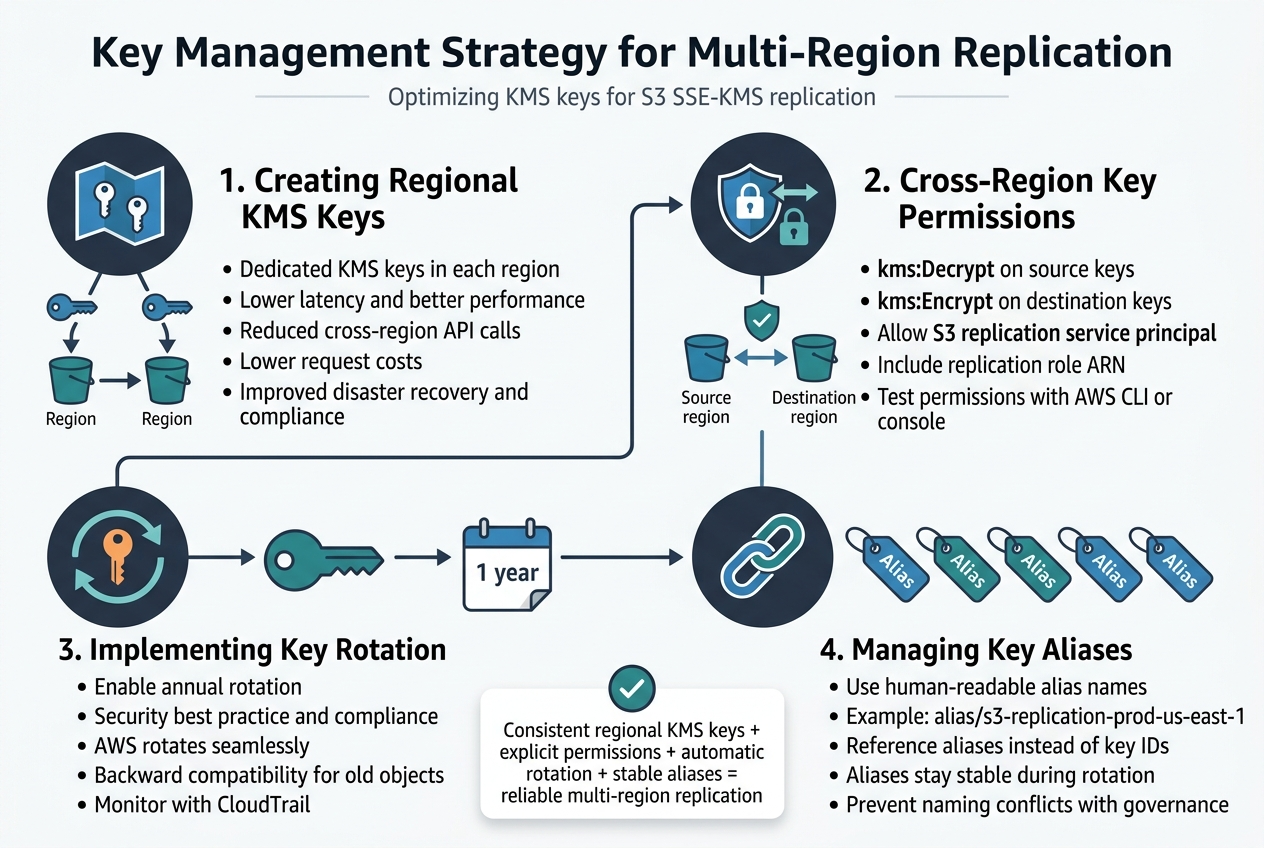
Establishing dedicated KMS keys in each target region dramatically improves S3 SSE-KMS replication performance and reduces latency. When you create region-specific keys rather than relying on cross-region key access, your replication process avoids the overhead of cross-region API calls during encryption operations. This approach also provides better cost control since you’re not paying for cross-region KMS requests on every object replication.
Regional keys offer enhanced disaster recovery capabilities and compliance benefits. If one region experiences service disruptions, your replicated data remains accessible using local KMS infrastructure. Create identical key policies across regions to maintain consistent access patterns while ensuring each key serves its regional workload efficiently.
Establishing Cross-Region Key Permissions
Cross-region replication requires carefully configured IAM policies that grant the replication service access to both source and destination KMS keys. Your replication role needs kms:Decrypt permissions on source region keys and kms:Encrypt permissions on destination region keys. The key policies must explicitly allow the S3 replication service principal to perform these operations.
Resource-based key policies should include the replication role ARN and specify the exact S3 service principals. This granular approach prevents unauthorized access while enabling seamless replication. Test permissions thoroughly using the AWS CLI or console before implementing in production environments.
Implementing Key Rotation Policies
Automatic key rotation strengthens your security posture without disrupting active replication processes. Enable annual rotation on all regional KMS keys used for S3 replication to meet compliance requirements and security best practices. AWS handles rotation seamlessly, maintaining backward compatibility with previously encrypted objects while using new key material for future operations.
Configure rotation schedules consistently across regions to maintain operational simplicity. Monitor rotation events through CloudTrail to ensure successful completion and update any hardcoded key references in your applications. Automated rotation eliminates the operational burden of manual key management while maintaining strong encryption standards.
Managing Key Aliases for Simplified Access
KMS key aliases provide human-readable names that simplify key management across multiple regions and environments. Create consistent alias naming conventions like alias/s3-replication-prod-us-east-1 to clearly identify purpose, environment, and region. This approach makes troubleshooting easier and reduces the risk of referencing incorrect keys in replication configurations.
Update replication rules to reference aliases instead of key IDs whenever possible. Aliases remain stable even when underlying keys are rotated or replaced, reducing maintenance overhead. Establish alias governance policies to prevent naming conflicts and ensure team members can easily identify the correct keys for their specific use cases.
Configuring Replication Rules for SSE-KMS Objects
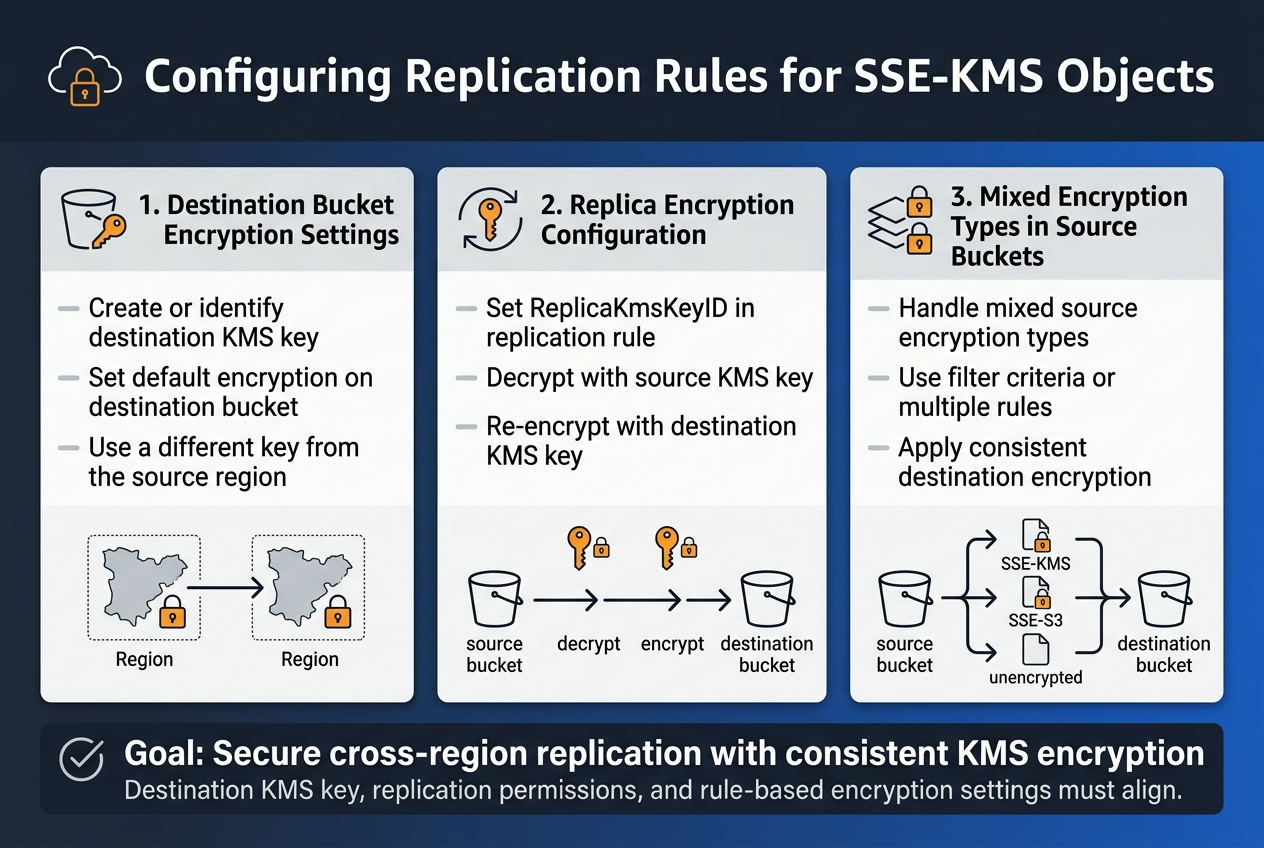
Setting Up Destination Bucket Encryption Settings
Before configuring S3 cross-region replication with SSE-KMS, ensure your destination bucket has the appropriate encryption settings. The destination bucket must have access to a KMS key in its region, either through a customer-managed key or AWS-managed S3 key. Create or identify the KMS key that will encrypt replicated objects, and verify that the replication role has the necessary permissions to use this key for encryption operations.
Configure the destination bucket’s default encryption settings to use your chosen KMS key. This ensures consistent encryption behavior for all replicated objects. Remember that the destination KMS key must be different from the source key since KMS keys are region-specific, making proper key management essential for successful S3 SSE-KMS replication across regions.
Defining Replica Encryption Configuration
Within your S3 replication configuration, specify the encryption settings for replica objects using the ReplicaKmsKeyID parameter. This parameter tells S3 which KMS key to use when encrypting objects in the destination bucket. The replication service will automatically decrypt objects from the source bucket using the source KMS key and re-encrypt them using the specified destination key.
Configure the EncryptionConfiguration block in your replication rule to define how replicated objects should be encrypted. You can choose to maintain the same encryption type as the source or specify a different encryption method for the destination. This flexibility allows you to adapt your S3 CRR with SSE-KMS setup to meet different security requirements across regions.
Handling Mixed Encryption Types in Source Buckets
Source buckets often contain objects with different encryption types – some encrypted with SSE-KMS, others with SSE-S3, and some unencrypted. Design your replication rules to handle this diversity by using filter criteria or multiple replication rules with different encryption configurations. This approach ensures that each object type receives appropriate treatment during the replication process.
Set up conditional encryption logic in your replication configuration to apply different destination encryption settings based on source object properties. You might encrypt all replicated objects with SSE-KMS regardless of their source encryption status, or maintain the original encryption type while adapting the keys for the destination region. This strategy provides consistency in your cross-region replication configuration while maintaining security standards.
Troubleshooting SSE-KMS Replication Failures
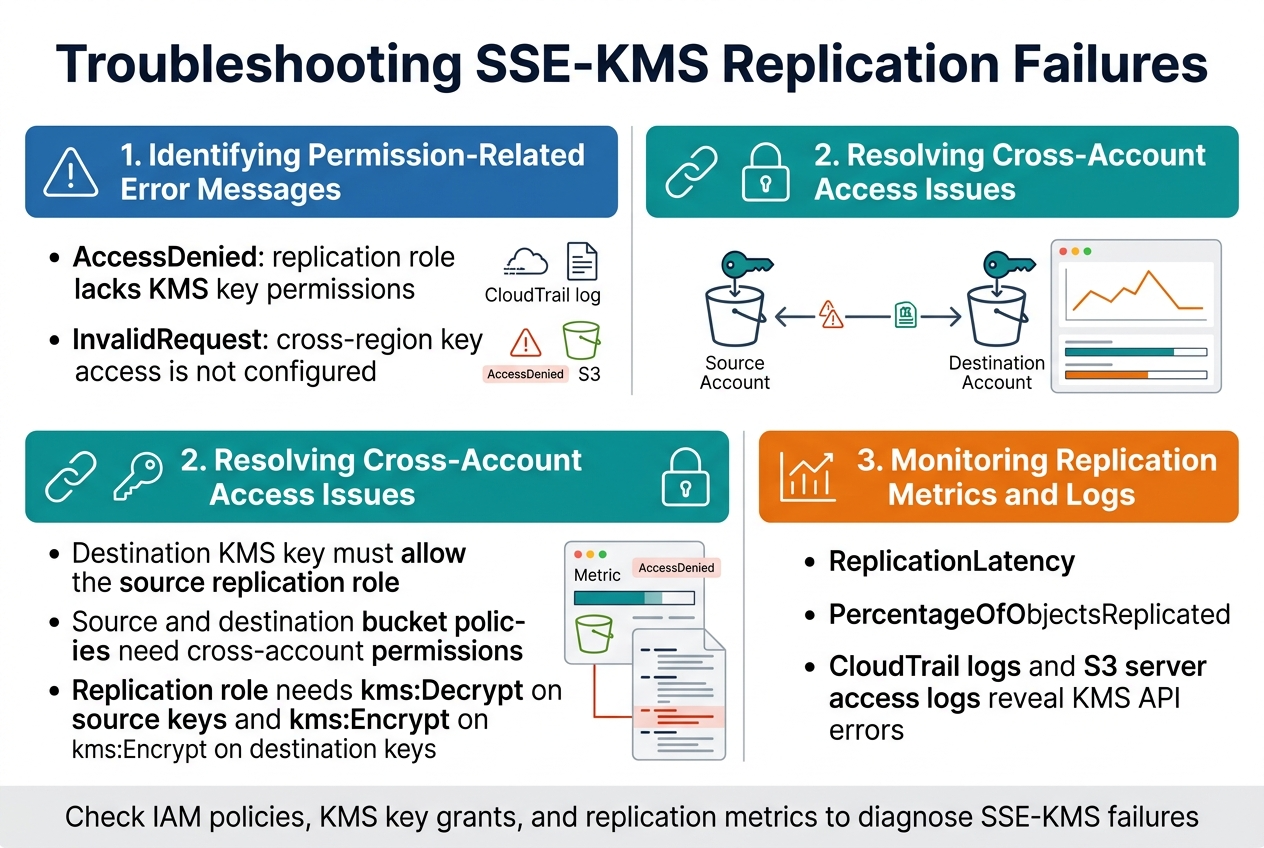
Identifying Permission-Related Error Messages
When S3 SSE-KMS replication fails, permission errors typically appear in CloudTrail logs and replication metrics. Common error messages include “AccessDenied” when the replication role lacks KMS key permissions, and “InvalidRequest” when cross-region key access isn’t properly configured. The S3 console displays these failures under replication metrics, showing specific error codes that point to IAM policy misconfigurations or missing KMS key grants for the destination region.
Resolving Cross-Account Access Issues
Cross-account SSE-KMS replication requires careful coordination between KMS key policies and IAM roles. The destination account’s KMS key must explicitly allow the source account’s replication role to use encryption and decryption operations. Resource-based policies on both the source and destination buckets need proper cross-account permissions, while the replication role must have “kms:Decrypt” permissions for source keys and “kms:Encrypt” permissions for destination keys across regions.
Monitoring Replication Metrics and Logs
CloudWatch metrics like “ReplicationLatency” and “PercentageOfObjectsReplicated” help track S3 CRR with SSE-KMS performance. Enable detailed replication metrics in the S3 console to monitor failed object counts and identify patterns in encryption-related failures. CloudTrail logs provide granular insights into KMS API calls during replication, while S3 server access logs capture detailed error responses that help diagnose specific SSE-KMS encryption challenges during cross-region replication operations.
Best Practices for Secure and Efficient SSE-KMS Replication
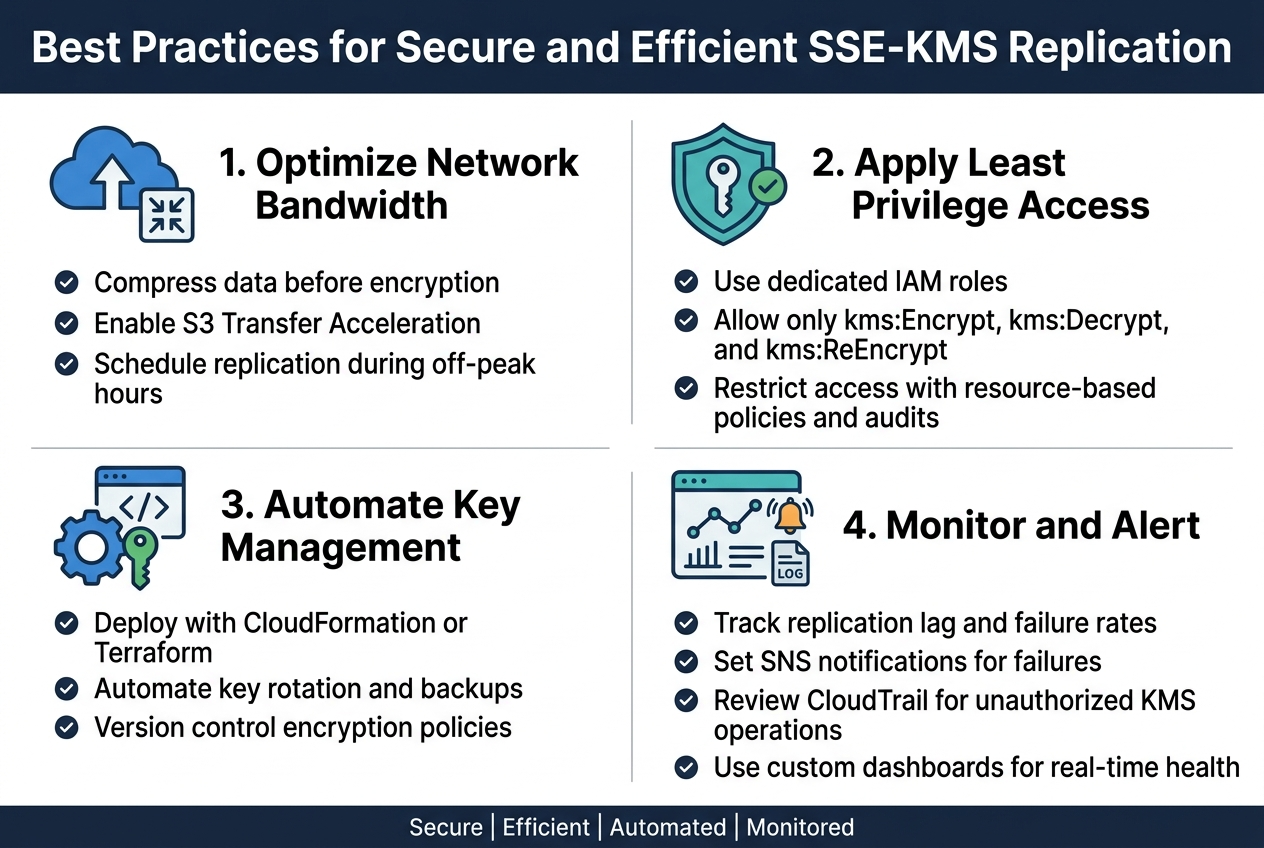
Optimizing Network Bandwidth for Encrypted Transfers
Compressing data before encryption can significantly reduce transfer times for S3 cross-region replication. Enable S3 Transfer Acceleration to route traffic through CloudFront edge locations, providing faster upload speeds for large encrypted objects. Configure replication timing during off-peak hours to avoid network congestion and reduce costs associated with data transfer fees.
Implementing Least Privilege Access Principles
Create dedicated IAM roles for S3 SSE-KMS replication with minimal required permissions. Grant kms:Encrypt, kms:Decrypt, and kms:ReEncrypt access only to specific KMS keys used in source and destination regions. Use resource-based policies to restrict cross-account access and regularly audit permissions to prevent privilege creep across your AWS environment.
Automating Key Management Through Infrastructure as Code
Deploy KMS keys and replication configurations using CloudFormation or Terraform templates for consistent multi-region setups. Implement automated key rotation schedules and backup strategies through Infrastructure as Code. Version control your encryption policies to track changes and enable quick rollbacks when configuration issues arise during deployment.
Setting Up Comprehensive Monitoring and Alerting
Configure CloudWatch metrics to track replication lag, failure rates, and KMS key usage patterns across regions. Set up SNS notifications for replication failures and unusual encryption activity. Monitor CloudTrail logs for unauthorized KMS operations and create custom dashboards displaying real-time replication health metrics for proactive issue detection.
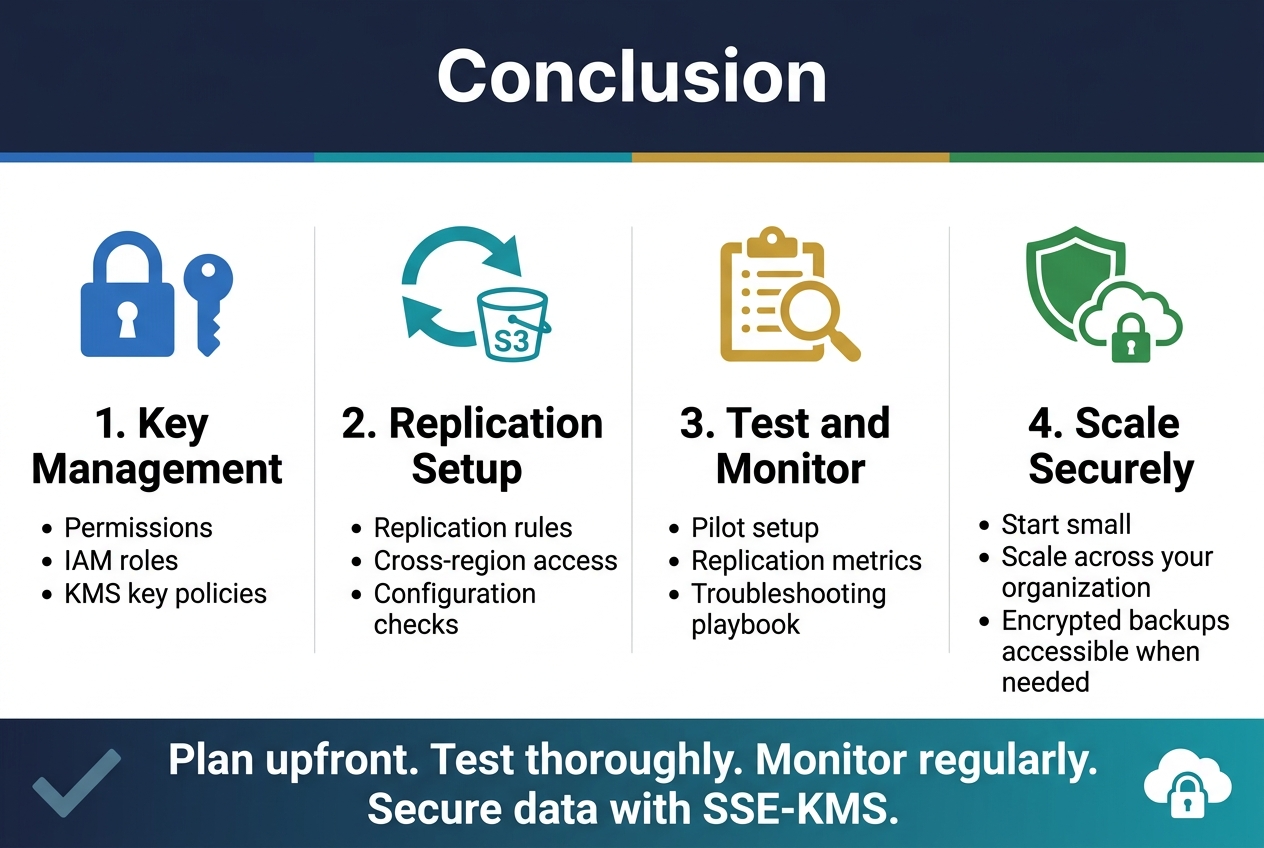
Setting up SSE-KMS encryption across multiple S3 regions brings its share of headaches, but the security benefits make it worth the effort. The main challenges revolve around key management permissions, replication rule configuration, and dealing with cross-region access issues. Getting your IAM roles right and making sure your KMS keys have the proper policies will save you hours of debugging down the road.
The key to success lies in planning your key management strategy upfront and testing your replication setup thoroughly before going live. Monitor your replication metrics regularly and keep your troubleshooting playbook handy for when things go sideways. Start small with a pilot setup, nail down the configuration, and then scale it across your organization. Your data will stay secure, and you’ll sleep better knowing your backups are encrypted and accessible when you need them most.
The post Handling SSE-KMS in S3 Replication: Challenges and Solutions first appeared on Business Compass LLC.
from Business Compass LLC https://ift.tt/nWme9Pf
via IFTTT
Comments
Post a Comment